Pentest Walkthrough
Pentest walkthrough - The Same Underlying Scanning Technology Trusted by Banks and Governments Worldwide. Get In Touch Today. Starting with the kickoff meeting you need to lay out a clear plan before you ever touch any. Ad Online CompTIA PenTest PT0-001 Prep. PenTest Skills Are in High Demand. This CTF was posted on VulnHub by Hadi Mene and is part of a Basic. A workflow or a generalized plan that each pentester typically follows. Buy Now Save. Increase Your Earnings Hiring Potential Today. Today we are going to solve another challenge from HackTheBox know as Knife design by mrkn16h7.
Basic Penetration Testing Walk Through For Beginners By Neera Jn Medium
Ad An Automated Pentesting Tool That Continuously Monitors Your Systems For Cyber Threats. Today I want to try my first CTF walkthrough. PenTest-Example A demonstratoin walkthrough of a pen test process using HTBs Bounty-Hunter with some normal dead ends as an example The preferred way to scan.
Show ImagePentest Walkthrough Scoping Planning Youtube
Get In Touch Today. In conjunction with neo4j the BloodHound client. Today I want to try my first CTF walkthrough.
Show ImagePenetration Testing Walkthrough Youtube
Get In Touch Today. Running those commands should start the console interface and allow you to change the default password similar to the Linux stage above. Get In Touch Today.
Show ImageBasic Pentesting 2 Walkthrough Archives Ceos3c
Basic Pentesting 1 Walkthrough. It is clear from the above-mentioned steps and processes that performing AWS penetration testing is vast and involves knowledge in. Today I want to try my first CTF walkthrough.
Show ImageBasic Pentesting 1 Walkthrough Vulnhub By Dinidhu Jayasinghe Infosec Write Ups
Ad An Automated Pentesting Tool That Continuously Monitors Your Systems For Cyber Threats. I am looking for more resources that would help me formulate a. Ad An Automated Pentesting Tool That Continuously Monitors Your Systems For Cyber Threats.
Show ImageTryhackme Basic Pentesting Walkthrough Youtube
HTB Walkthrough. Understand Real-World Risks Impacts of System-Vulnerabilities. Understand Real-World Risks Impacts of System-Vulnerabilities.
Show ImageVulnhub Basic Pentesting 1 Walkthrough
Your goal is to remotely attack the VM and gain. Today we are going to solve another challenge from HackTheBox know as Knife design by mrkn16h7. Running those commands should start the console interface and allow you to change the default password similar to the Linux stage above.
Show ImageBasic Pentesting 1 Walkthrough
Includes Virtual Labs Practice Exams Coaching More. Today we are going to solve another challenge from HackTheBox know as Knife design by mrkn16h7. Get In Touch Today.
Show ImageTryhackme Basic Pentesting Walkthrough By Vadim Polovnikov Infosec Write Ups
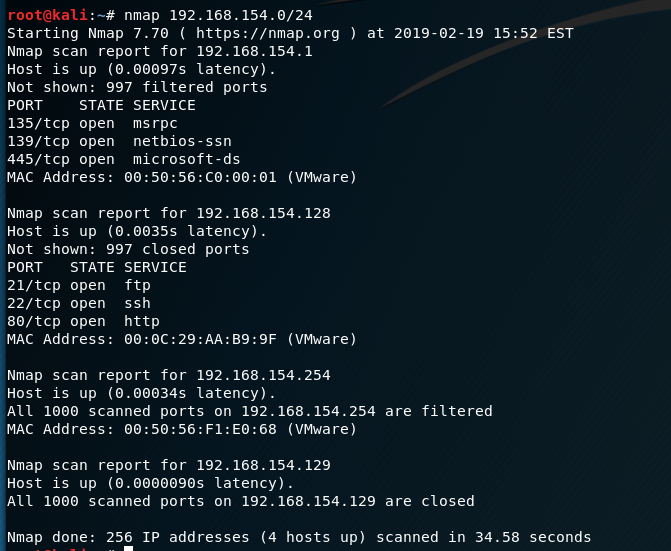
I choose the relatively new Basic Pentesting 1 VM from Vulnhub. 2 CTF walkthrough. Increase Your Earnings Hiring Potential Today.
Show ImageBasic Pentesting 2 Ctf Walkthrough Infosec Resources
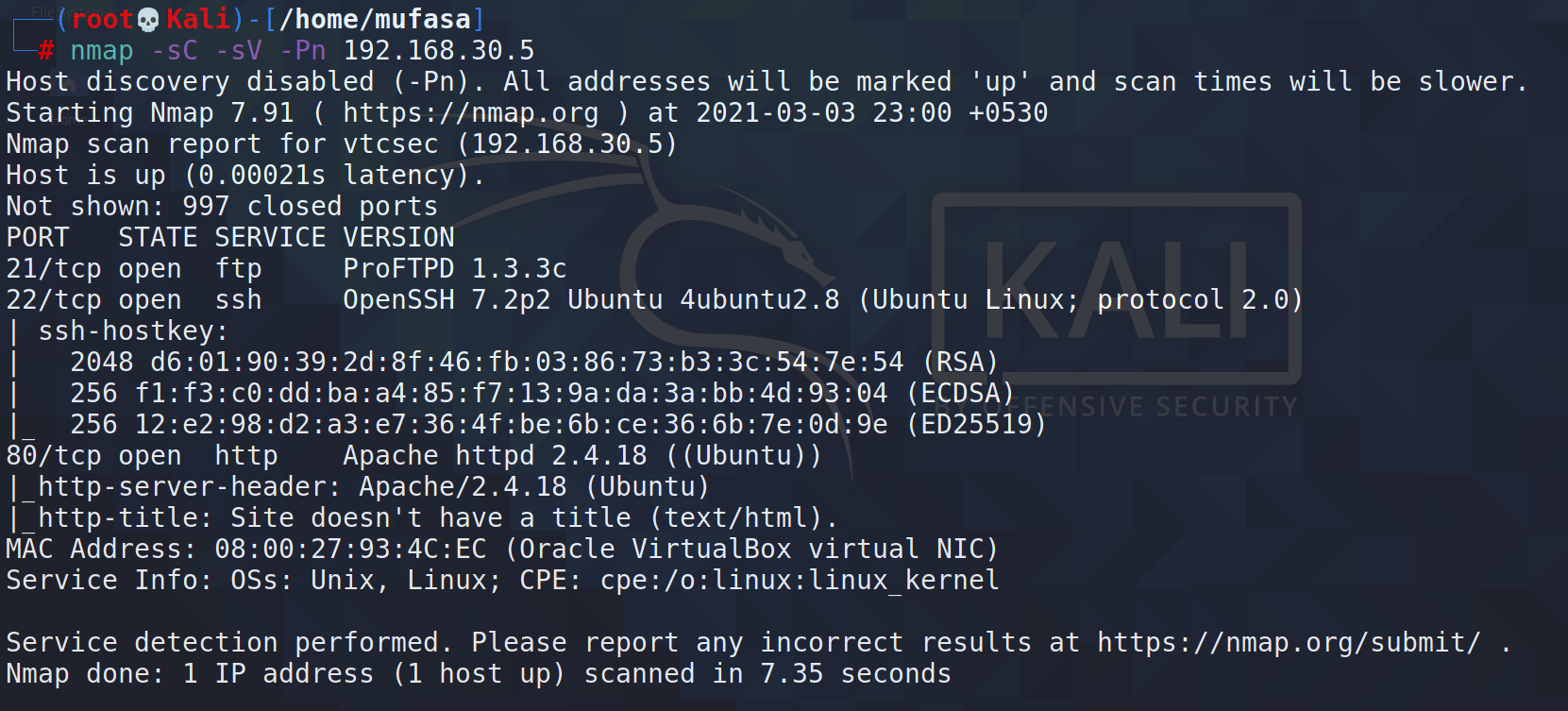
This CTF is aimed towards beginners and the. In conjunction with neo4j the BloodHound client. PenTest-Example A demonstratoin walkthrough of a pen test process using HTBs Bounty-Hunter with some normal dead ends as an example The preferred way to scan.
Show ImageAd Online CompTIA PenTest PT0-001 Prep. Today we are going to solve another challenge from HackTheBox know as Knife design by mrkn16h7. This CTF is aimed towards beginners and the. Buy Now Save. Ad Save 36 on PenTest Exam Voucher Certmaster Training Bundle. August 29 2021 by pentestsky. In this article we will try to solve another Capture the Flag CTF challenge. If youre a beginner you should hopefully find the difficulty of the VM to be just right. The Same Underlying Scanning Technology Trusted by Banks and Governments Worldwide. Get The Skills to Stay Competitive.
AWS Penetration Testing Provider Astra Security. Ad An Automated Pentesting Tool That Continuously Monitors Your Systems For Cyber Threats. Ad Gain a Complete Understanding of Exploitable Vulnerabilities in Your Environment. In conjunction with neo4j the BloodHound client. Increase Your Earnings Hiring Potential Today. Get In Touch Today. 2 CTF walkthrough. Running those commands should start the console interface and allow you to change the default password similar to the Linux stage above. Ad Certified USA Based Pen Testing. Ad An Automated Pentesting Tool That Continuously Monitors Your Systems For Cyber Threats.
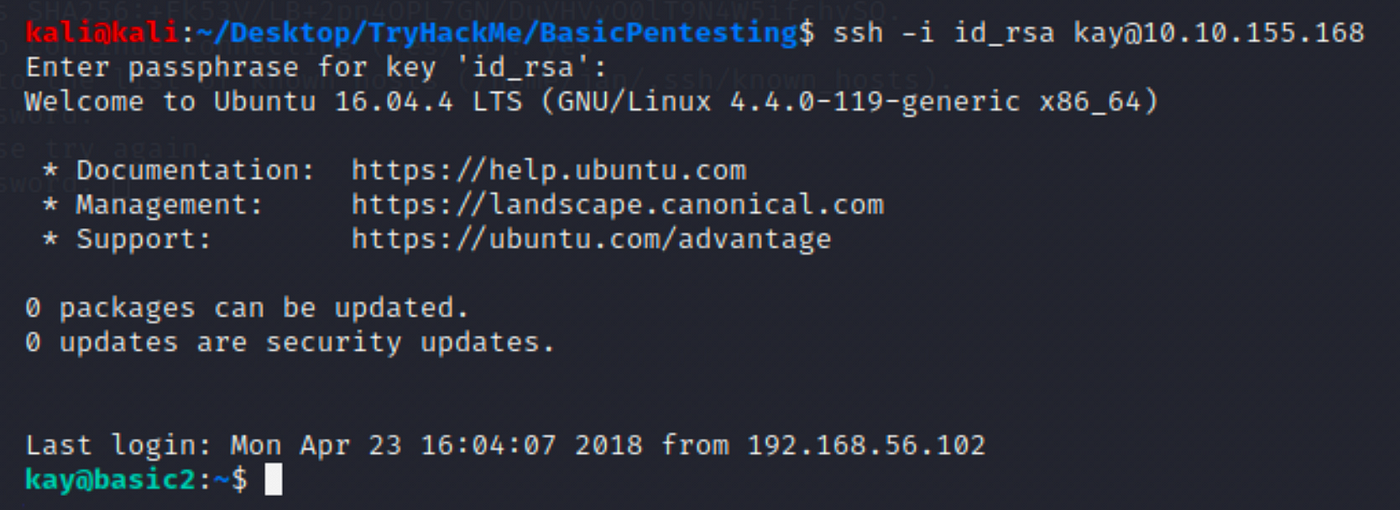
This CTF was posted on VulnHub by Hadi Mene and is part of a Basic. Includes Virtual Labs Practice Exams Coaching More. Get In Touch Today. Includes Virtual Labs Practice Exams Coaching More. This VM is specifically intended for newcomers to penetration testing. I am looking for more resources that would help me formulate a. Penetration Testing pen testing or ethical hacking is the process of assessing an application or infrastructure for vulnerabilities in an attempt to exploit those vulnerabilities and. I choose the relatively new Basic Pentesting 1 VM from Vulnhub. Today I want to try my first CTF walkthrough. Your goal is to remotely attack the VM and gain.
PenTest Skills Are in High Demand. Basic Pentesting 1 Walkthrough. Ad Online CompTIA PenTest PT0-001 Prep. PenTest-Example A demonstratoin walkthrough of a pen test process using HTBs Bounty-Hunter with some normal dead ends as an example The preferred way to scan. I have found one already. Starting with the kickoff meeting you need to lay out a clear plan before you ever touch any. Free 7 Day Trial - No CC Required. Ad Gain a Complete Understanding of Exploitable Vulnerabilities in Your Environment. Free 7 Day Trial - No CC Required. Cross-site request forgery also known as CSRF is a web security vulnerability that allows an attacker to induce users to perform actions that they do not intend to perform.
This video covers the scoping and planning phase of a pentest. The Same Underlying Scanning Technology Trusted by Banks and Governments Worldwide. HTB Walkthrough. Get The Skills to Stay Competitive. A workflow or a generalized plan that each pentester typically follows. Understand Real-World Risks Impacts of System-Vulnerabilities. Understand Real-World Risks Impacts of System-Vulnerabilities. It is clear from the above-mentioned steps and processes that performing AWS penetration testing is vast and involves knowledge in.